DNS以及域名分发布式数据库相关知识
一、 DNS相关介绍
1. DNS(Domain Name Service):域名解析服务协议
2. 通常监听段脱口:UDP:53 和 TCP: 53
3. 实现应用程序:BIND(Berkeley Internet Name Domain), PowerDNS, etc
4. DNS服务主要工作于域名解析分布式数据库, 用来做域名IP之间的解析
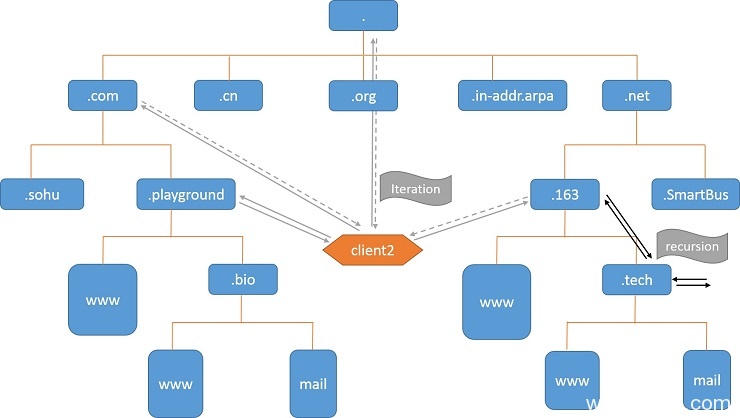
二、 域名分布式数据库
1. 根域:.
2. 一级域: 组织域(.com .org .mil ; 国家域 (.cn, .tw .jp .us); 反向域 (.in-addr.arpa )
3. 解析方式:
- FQDN (Full Qualified Domain Name) –> IP : 正向解析
- IP –> FQDN:反向解析
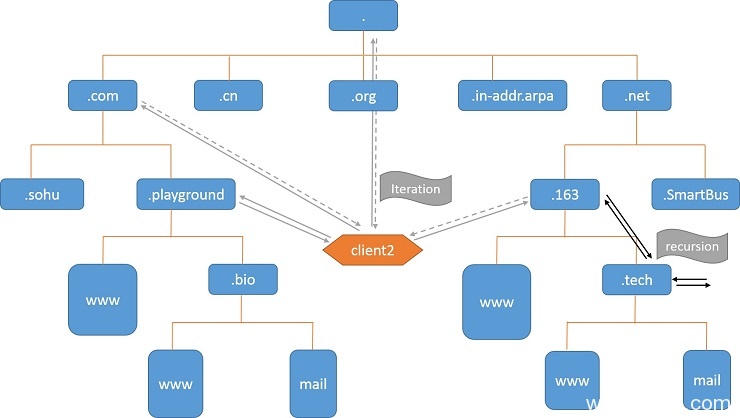
4. 递归与迭代
- 递归:DNS请求被服务器接收后,如果属于此服务器管辖范围则请求上级服务器依次传递请求,并且依次传递结果给发出请求的主机。客户机指向的服务器一定给递归服务。
- 迭代: DNS请求被服务器接收后,如果不是自己管辖范围,让客户端访问根域服务器,然后跟域通知客户端去访问下级服务器,直到最后客户端访问管辖请求域名的服务器为止。
5. 资源记录(Resource Record):资源记录用用于存储域名解析数据记录, 几种记录类型如下
- SOA:Start Of Authority, 其实授权:用于声明本地域被授权
- NS:Name Server, 域名服务器:用于记录域名服务器信息
- MX:Mail eXchanger,邮件交换器:记录邮件服务器信息
- A:Address, FQDN –> IP
- PTR:PoiTeR,IP –> FQDN
- AAAA:Address, FQDN –> IPv6
- CNAME: Canonical Name, 咩名记录
6. 域(Domain) 和 区域(zone)
- 域(Domain):逻辑概念
- 区域(zone):物理概念,特指存储资源记录的硬件设备,如文本文件,或者数据库
- 正向区域和反向区域域不能存储在一个文件或者数据库中,由于解析技术不同
7. DNS服务器类型
8. DNS数据文件格式(bind为例):文本文件,包含资源记录或宏定义
ng-bsh"> 资源记录的格式:
name [ttl] IN RRtype Value
例子:
www 600 IN A 1.2.3.4
www.playground.com. 600 IN A 1.2.3.4
SOA: 只能有一个
name: 区域名称, 通常可以简写为@,例如:magedu.com.
value: 主DNS服务器的FQDN
注意:SOA必须是区域数据库文件第一条记录
例子:@ 600 IN SOA ns.playground.com. dnsadmin.playground. (
serial number ;序列号,十进制数字,不能超过10位,通常使用日期,例如2014031001
refresh time ;刷新时间,即每隔多久到主服务器检查一次
retry time ;重试时间,应该小于refresh time
expire time ;过期时间
negative answer ttl ;否定答案的ttl
)
NS:可以有多条
name: 区域名称,通常可以简写为@
value: DNS服务器的FQDN(可以使用相对名称)
例子:
@ 600 IN NS ns
A: 只能定义在正向区域数据库文件中
name: FQDN(可以使用相对名称)
value: IP
例子:
www 600 IN A 1.2.3.4
www 600 IN A 1.2.3.5
www 600 IN A 1.2.3.4
ftp 600 IN A 1.2.3.4
MX: 可以有多个
name: 区域名称,用于标识smtp服务器
value: 包含优先级和FQDN
优先级:0-99, 数字越小,级别越高;
例子:
@ 600 IN MX 10 mail
@ 600 IN MX 20 mail2
CNAME:
name: FQDN
value: FQDN
例子:
ftp IN CNAME www
mail IN CNAME www
PTR: IP-->FQDN, 只能定义在反向区域数据文件中,反向区域名称为逆向网络地址加.in-addr.arpa.后缀组成
name: IP, 逆向的主机地址,例如172.16.100.7的name为7.100,完全格式为7.100.16.172.in-addr.arpa.
value: FQDN
例子:
4.3.2 600 IN PTR www.playground.com.
9. 区域传送:
- 辅助DNS服务器从主DNS服务器或其他辅助DNS服务器请求传输数据的过程
- 完全区域传送:传送区域的所有数据,AXFER
- 增量区域传送:传送区域中改变的数据不符,IXFER
DNS程序软件bind简介
一、 BIND简介
1. BIND: www.isc.org
2. 服务程序名称: named, 由named:named 执行
3. bind安装包组
bind.x86_64 : 包含bind应用程序
bind-chroot.x86_64 : 支持change root 机制
bind-devel.i686 : 32bit bind开发包
bind-devel.x86_64 : 64bit bind开发包
bind-dyndb-ldap.x86_64 : 支持动态数据库
bind-libs.i686 : bind相关库文件
bind-libs.x86_64 : 64bit 库文件
bind-sdb.x86_64 : 支持数据库接口
bind-to-tinydns.x86_64 : 微型DNS服务器程序
bind-utils.x86_64 : 工具包
二、主配置文件和区域文件 /etc/named.conf, /var/named/
1. 必须的三个区域: 跟 . localhost 127.0.0.1
主配置文件:
options {
// 全局选项
};
zone "ZONE name" {
// 定义区域
};
logging {
// 定义日志系统
};
2. 域类型
- hint:缓存域,用于缓存服务器
- master:主域,用于主服务器
- slave:从域,用于从服务器
- forward:转发域
三、 named服务正向以及反向解析事例
举例: 添加正向域域.playground 和 反向域233.168.192.in-addr.arpa
mail, 192.168.98.12
www 192.168.98.13
pop –> mail
ftp –> www
dns: 192.168.233.128
1. 编辑主配置文件
options {
# listen-on port 53 { 127.0.0.1; }; # 注释后监听所有ip的53号端口
# listen-on-v6 port 53 { ::1; }; # 注释后监听所有ipv5的53号端口
directory "/var/named"; # 区域文件所在目录
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
# allow-query { 127.0.0.1; 192.168.233.128; 192.168.233.131; }; # 允许访问的白名单,注释后允许所有IP访问
recursion yes; # 是否提供递归
# dnssec-enable yes;
# dnssec-validation yes;
# dnssec-lookaside auto;
/* Path to ISC DLV key */
bindkeys-file "/etc/named.iscdlv.key";
managed-keys-directory "/var/named/dynamic";
};
logging {
channel default_debug {
file "data/named.run";
severity dynamic;
};
};
zone "." IN {
type hint;
file "named.ca";
};
include "/etc/named.rfc1912.zones"; # 读取的域文件信息
#include "/etc/named.root.key"; # 与远程操控相关
2. 添加新的域 .playground.com于/etc/named.rfc1912.zones 中
## 添加正向区域
zone "playground.com" IN {
type master;
file "playground.zone";
};
## 添加反向区域
zone "98.168.192.in-addr.arpa" IN {
type master;
file "192.168.98.zone";
};
3. 编辑区域文件
## 在/var/named/编辑正向区域文件保存为 playground.zone, 与配置文件中输入的文件名一致
$TTL 600
@ IN SOA dns.playground.com. dnsadmin.playground.com. (
20150305
1H
5M
3D
12H )
@ IN NS dns
@ IN MX 10 mail
dns IN A 192.168.233.128
mail IN A 192.168.98.12
www IN A 192.168.98.13
ftp IN CNAME www
pop IN CNAME www
## 在/var/named/编辑反向区域文件保存为 192.168.233.zone, 与配置文件中输入的文件名一直
$TTL 600
@ IN SOA dns.playground.com. dnsadmin.playground.com.(
20150305
1H
5M
3D
12H )
@ IN NS dns.playground.com.
128 IN PTR dns.playground.com.
12 IN PTR mail.playground.com.
13 IN PTR www.playground.com.
ns IN A 192.158.98.128
mail IN A 192.168.98.12
www IN A 192.168.98.13
4. 修改配置文件属组属组为named:named, 权限位640
## 如果不修改属主属组,named将无法读取配置文件,由于named服务是通过named用户启动
chown named:named /etc/named.rfc1912.zones
chown named:named /etc/named.conf
## 修改配置文件权限,主要为了安全,即便named服务被攻破,也不至于重要信息泄露
chmod 640 /etc/named.conf
chmod 640 /etc/named.rfc1912.zones
chown named:named /var/named/playground.zone
chmod 640 /var/named/playground.zone
5. 启动服务,查看TCP/UDP 53号端口是否被监听, 查看/var/log/message
ss -tunl | grep ":53"
udp UNCONN 0 0 192.168.233.128:53 *:*
udp UNCONN 0 0 172.25.137.40:53 *:*
udp UNCONN 0 0 127.0.0.1:53 *:*
tcp LISTEN 0 3 192.168.233.128:53 *:*
tcp LISTEN 0 3 172.25.137.40:53 *:*
tcp LISTEN 0 3 127.0.0.1:53 *:*
service named configtest ## 测试配置文件语法是否正确
zone localhost.localdomain/IN: loaded serial 0
zone localhost/IN: loaded serial 0
zone 1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.ip6.arpa/IN: loaded serial 0
zone 1.0.0.127.in-addr.arpa/IN: loaded serial 0
zone 0.in-addr.arpa/IN: loaded serial 0
zone playground.com/IN: loaded serial 20150305
zone 98.168.192.in-addr.arpa/IN: loaded serial 20150305
service named start ## 启动服务
Starting named: [ OK ]
tail /var/log/messages ## 查看服务日志
Mar 13 22:40:26 www named[47455]: zone 0.in-addr.arpa/IN: loaded serial 0
Mar 13 22:40:26 www named[47455]: zone 1.0.0.127.in-addr.arpa/IN: loaded serial 0
Mar 13 22:40:26 www named[47455]: zone 98.168.192.in-addr.arpa/IN: loaded serial 20150305
Mar 13 22:40:26 www named[47455]: zone 1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.ip6.arpa/IN: loaded serial 0
Mar 13 22:40:26 www named[47455]: zone playground.com/IN: loaded serial 20150305
Mar 13 22:40:26 www named[47455]: zone localhost.localdomain/IN: loaded serial 0
Mar 13 22:40:26 www named[47455]: zone localhost/IN: loaded serial 0
Mar 13 22:40:26 www named[47455]: managed-keys-zone ./IN: loaded serial 288
Mar 13 22:40:26 www named[47455]: zone 98.168.192.in-addr.arpa/IN: sending notifies (serial 20150305)
Mar 13 22:40:26 www named[47455]: running
6 使用dig命令测试
dig www.playground.com @192.168.233.128 ## 测试正向解析
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.30.rc1.el6_6.1 <<>> www.playground.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 34061
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 1
;; QUESTION SECTION:
;www.playground.com. IN A
;; ANSWER SECTION:
www.playground.com. 600 IN A 192.168.98.13
;; AUTHORITY SECTION:
playground.com. 600 IN NS dns.playground.com.
;; ADDITIONAL SECTION:
dns.playground.com. 600 IN A 172.25.137.40
;; Query time: 0 msec
;; SERVER: 127.0.0.1#53(127.0.0.1)
;; WHEN: Fri Mar 13 22:47:49 2015
;; MSG SIZE rcvd: 86
dig -x 192.168.98.13 @192.168.233.128 ## 测试反向解析
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.30.rc1.el6_6.1 <<>> -x 192.168.98.13
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 17843
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 0
;; QUESTION SECTION:
;13.98.168.192.in-addr.arpa. IN PTR
;; ANSWER SECTION:
13.98.168.192.in-addr.arpa. 600 IN PTR www.playground.com.
;; AUTHORITY SECTION:
98.168.192.in-addr.arpa. 600 IN NS ns.playground.com.
;; Query time: 0 msec
;; SERVER: 127.0.0.1#53(127.0.0.1)
;; WHEN: Fri Mar 13 22:48:07 2015
;; MSG SIZE rcvd: 93
四、 区域传送以及从服务器配置

1. dig 模拟完全区域传送
# dig -t axfr playground.com @192.168.233.128
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.30.rc1.el6_6.1 <<>> -t axfr playground.com @192.168.233.128
;; global options: +cmd
playground.com. 600 IN SOA dns.playground.com. dnsadmin.playground.com. 20150305 3600 300 259200 43200
playground.com. 600 IN NS dns.playground.com.
playground.com. 600 IN MX 10 mail.playground.com.
dns.playground.com. 600 IN A 172.25.137.40
ftp.playground.com. 600 IN CNAME www.playground.com.
mail.playground.com. 600 IN A 192.168.98.12
pop.playground.com. 600 IN CNAME www.playground.com.
www.playground.com. 600 IN A 192.168.98.13
playground.com. 600 IN SOA dns.playground.com. dnsadmin.playground.com. 20150305 3600 300 259200 43200
;; Query time: 16 msec
;; SERVER: 192.168.233.128#53(192.168.233.128)
;; WHEN: Fri Mar 13 23:30:15 2015
;; XFR size: 9 records (messages 1, bytes 240)
2. 主从兼容关系:主服务器bind版本可以低于从服务器bind版本
3. 向区域文件中添加从服务器关键两步奏:
- 往上级获得授权(这里指的DNS上级父域服务器)
- 在主区域文件中为从服务器添加NS记录和对应的A或PTR记录
4. 从服务器,事例。
假设:有另一个主机,IP地址为192.168.233.129,作为192.168.233.128(接续上面的事例)的从服务器。
首先在主DNS服务器的区域文件中,添加从服务器的NS记录
## 正向,添加从服务器的NS记录
@ IN NS ns
ns IN A 192.168.233.129
## 反向, 添加从服务器的NS记录
@ IN NS ns.playground.com.
129 IN PTR ns.playground.com.
## 添加完成后,如果不是使用named用户操作,一定注意修把文件属主属组改为named:named, 另外修改一下序列号
service named reload ## 重启服务
然后在从服务器主机上bind配置文件中添加,与主服务器相同的两个正反向域
## 从服务器正向域
zone "playground.com" IN {
type slave;
masters { 192.168.233.128; };
file "slaves/playground.com.zone";
};
## 从服务器反向域
zone "233.168.192.in-addr.arpa" IN {
type slave;
masters { 192.168.233.128; };
file "slaves/192.168.233.com.zone";
};
## 重启服务
service named restart
查看日志文件,同步过来的区域文件,尝试用从服务器解析
tail /var/log/message
Mar 17 03:59:52 www named[2533]: running
Mar 17 03:59:52 www named[2533]: zone 233.168.192.in-addr.arpa/IN: sending notifies (serial 20150305)
Mar 17 03:59:52 www named[2533]: zone playground.com/IN: sending notifies (serial 3934520385)
ls /var/named/slaves ## 查看区域文件是否成功同步过来
-rw-r--r--. 1 named named 482 Mar 17 03:47 192.168.233.com.zone
-rw-r--r--. 1 named named 497 Mar 17 03:54 playground.com.zone
dig -t A www.playground.com @192.168.233.129 ## 尝试解析
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.30.rc1.el6_6.1 <<>> -t A www.playground.com @192.168.233.129
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 17894
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 2, ADDITIONAL: 2
;; QUESTION SECTION:
;www.playground.com. IN A
;; ANSWER SECTION:
www.playground.com. 600 IN A 192.168.98.13
;; AUTHORITY SECTION:
playground.com. 600 IN NS dns.playground.com.
playground.com. 600 IN NS ns.playground.com.
;; ADDITIONAL SECTION:
dns.playground.com. 600 IN A 172.25.137.40
ns.playground.com. 600 IN A 192.168.233.129
;; Query time: 0 msec
;; SERVER: 192.168.233.129#53(192.168.233.129)
;; WHEN: Tue Mar 17 04:02:31 2015
;; MSG SIZE rcvd: 119
五、 子域授权
1. BIND子域授权的实现:首先需要在父域区域文件中添加胶水记录(glue record)说要授权的子域信息和主机IP,父域区域文件中需要添加如下几项
授权的子区域域名称
子区域的名称服务器
子区域的名称服务器IP地址
例子:
bio.playground.com. IN NS dns.bio.playground.com.
bio.playground.com. IN NS ns2.bio.playground.com.
dns.bio.playground.com. IN A 172.16.200.21
ns2.bio.playground.com. IN A 172.16.200.22
2. 配置区域转发:转发域
解析某本机不负责的区域内的名称时不转发给跟,而是转发给指定主机
zone "ZONE NAME" IN {
type forward;
forwarders { DNS_SERVER; };
forward only|first;
};
配置转发方式:
转发非本机负责解析的所有区域:
options {
forward only|first;
forwarders { IP; }
};
转发某特定区域:
zone "特定区域" IN {
type forward;
forwarders { IP; }
forward only|first;
};
3. ACL:bind实现支持的访问控制列表
acl ACL_NAME {
172.16.0.0/16;
192.168.0.0/24
127.0.0.0/8;
};
访问控制列表只有定义后才能使用;通常acl要定义在named.conf的最上方;
BIND有四个内置的acl:
any: 任何主机
none: 无一主机
local: 本机
localnet: 本机的所在的网络
4. 实例, 接续上面上面的例子,
父域为playground.com. 地址为192.168.233.128,
需要授权给另一台主机192.168.233.129,
子域bio.playground.com. 并且要求子域服务器可以解析父域其他域名
在父域playground.com区域文件中添加胶水记录
bio IN NS ns.bio
ns.bio IN A 192.168.233.129
在子域主机配置文件中添加这个域
zone "bio.playground.com" IN {
type master;
file "bio.playground.com.zone";
};
在子域主机编辑并添加/var/named/bio.playground.com.zone 子域区域文件, 并修改权限和属主属组(named:named)
@ IN SOA ns.bio.playground.com. nsbioadmin.playground.com. (
20150309001
1H
5M
3D
12H )
@ IN NS ns.bio.playground.com.
@ IN MX 10 mail.bio.playground.com.
ns IN A 192.168.233.129
mail IN A 192.168.233.140
www IN A 192.168.233.141
ftp IN A 192.168.233.142
pop IN CNAME ftp
在子域配置文件中,添加转发域,使得子域主机可以解析父域域名
此时注意要开启父域配置文件中的recursion yes, 或者建立recursion白名单,这里笔者偷懒直接用recursion yes 解决,在生产条件下这样设定很不安全
zone "playground.com" IN {
type forward;
forwarders { 192.168.233.128; };
forward only;
};
重启或者重新载入父子域服务器后,尝试解析
在子域服务器上解析子域域名
dig www.bio.playground.com @192.168.233.129
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.30.rc1.el6_6.1 <<>> www.bio.playground.com @192.168.233.129
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 17622
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 1
;; QUESTION SECTION:
;www.bio.playground.com. IN A
;; ANSWER SECTION:
www.bio.playground.com. 43200 IN A 192.168.233.141
;; AUTHORITY SECTION:
bio.playground.com. 43200 IN NS ns.bio.playground.com.
;; ADDITIONAL SECTION:
ns.bio.playground.com. 43200 IN A 192.168.233.129
;; Query time: 0 msec
;; SERVER: 192.168.233.129#53(192.168.233.129)
;; WHEN: Tue Mar 17 17:16:39 2015
;; MSG SIZE rcvd: 89
## 在子域服务器上解析父域域名
dig www.playground.com @192.168.233.129
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.30.rc1.el6_6.1 <<>> www.playground.com @192.168.233.129
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 9272
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 1
;; QUESTION SECTION:
;www.playground.com. IN A
;; ANSWER SECTION:
www.playground.com. 600 IN A 192.168.98.13
;; AUTHORITY SECTION:
playground.com. 600 IN NS dns.playground.com.
;; ADDITIONAL SECTION:
dns.playground.com. 600 IN A 192.168.233.129
;; Query time: 15 msec
;; SERVER: 192.168.233.129#53(192.168.233.129)
;; WHEN: Tue Mar 17 17:18:02 2015
;; MSG SIZE rcvd: 86
两次解析结果差别在于flags, 如果在子域解析父域,则少一个aa flag说明不是权威答案,只是参考答案
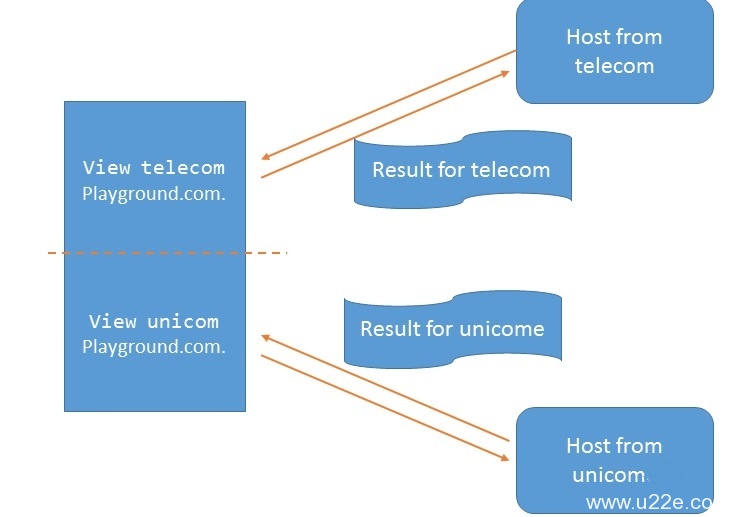
六、view视图, 实现主机对于不同IP访问对于同一域名产生不同的应答机制,用于解决不同网络间解析效率问题 ,需要注意的是,如果使用view则所有区域都必须在view中
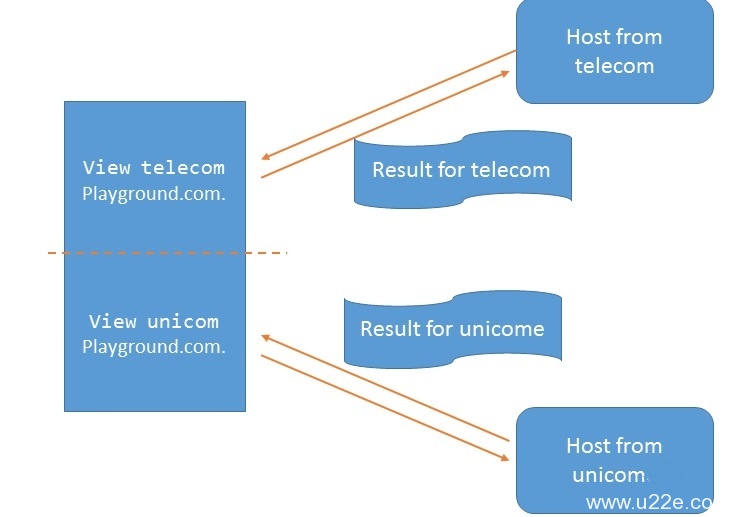
1. 语法格式如下
以中国移动和中国联通为例
acl telecom {
1.2.0.0/16;
4.5.8.0/24;
};
acl unicom {
};
view telecom {
match-clients { telecom; };
zone "playground.com" IN {
type master;
file "playground.com.telecom";
};
};
view unicom {
match-clients { unicom; };
recursion no;
zone "playground.com" IN {
type master;
file "playground.com.unicom";
};
};
view default {
match-clients { any; };
zone "playground.com" IN {
type master;
file "playground.com.unicom";
};
};
2. 实验事例,
假定有一个域,playground.com, 如果通过172.25.137.41访问则返回一组解析结果, 如果通过192.168.233.129 访问则返回另一组结果。
第一台主机,为DNS服务器, 拥有两个端口,192.168.233.128 和 172.25.137.40,这里笔者使用别名实现
另两台主句, 一台为192.168.233.129 一台为172.25.137.41
设置,DNS服务器IP
ifconfig eth0 192.168.233.128/24
ifconfig eth0:1 172.24.137.43/24
eth0 Link encap:Ethernet HWaddr 00:0C:29:E0:A2:0E
inet addr:192.168.233.128 Bcast:192.168.233.255 Mask:255.255.255.0
inet6 addr: fe80::20c:29ff:fee0:a20e/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:45186 errors:0 dropped:0 overruns:0 frame:0
TX packets:32619 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:18628316 (17.7 MiB) TX bytes:2974242 (2.8 MiB)
eth0:1 Link encap:Ethernet HWaddr 00:0C:29:E0:A2:0E
inet addr:172.25.137.40 Bcast:172.25.137.255 Mask:255.255.255.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
修改bind配置文件,添加view
acl localArea {
127.0.0.1/4;
};
acl vm1 {
192.168.233.131/24;
192.168.233.128/24;
};
acl vm2 {
172.25.137.41/24;
172.25.137.40/24;
};
view localArea {
match-clients { localArea; };
zone "localhost.localdomain" IN {
type master;
file "named.localhost";
allow-update { none; };
};
zone "localhost" IN {
type master;
file "named.localhost";
allow-update { none; };
};
zone "1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.ip6.arpa" IN {
type master;
file "named.loopback";
allow-update { none; };
};
zone "1.0.0.127.in-addr.arpa" IN {
type master;
file "named.loopback";
allow-update { none; };
};
zone "0.in-addr.arpa" IN {
type master;
file "named.empty";
allow-update { none; };
};
};
view vm1 {
match-clients { vm1; };
zone "playground.com" IN {
type master;
file "playground.vm1";
};
zone "98.168.192.in-addr.arpa" IN {
type master;
file "192.168.98.vm1";
};
};
view vm2 {
match-clients { vm2; };
zone "playground.com" IN {
type master;
file "playground.vm2";
};
zone "137.25.172.in-addr.arpa" IN {
type master;
file "172.25.137.vm2";
};
};
view default {
match-clients { any;};
zone "." IN {
type hint;
file "named.ca";
};
};
编辑vm1的正反向域区域文件
## vm1这是正向域
$TTL 600
@ IN SOA dns.playground.com. dnsadmin.playground.com. (
20150305
1H
5M
3D
12H )
@ IN NS dns
@ IN MX 10 mail
dns IN A 192.168.233.128
mail IN A 192.168.98.12
www IN A 192.168.98.13
ftp IN CNAME www
pop IN CNAME www
## vm1这是反向域
$TTL 600
@ IN SOA dns.playground.com. dnsadmin.playground.com.(
20150305
1H
5M
3D
12H )
@ IN NS ns.playground.com.
128 IN PTR ns.playground.com.
12 IN PTR mail.playground.com.
13 IN PTR www.playground.com.
编辑vm2正反向域区域文件
## 这是vm2正向域
$TTL 600
@ IN SOA dns.playground.com. dnsadmin.playground.com. (
20150305
1H
5M
3D
12H )
@ IN NS dns
@ IN MX 10 mail
dns IN A 172.25.137.40
mail IN A 172.25.137.12
www IN A 172.25.137.13
ftp IN CNAME www
pop IN CNAME www
## 这是vm2反向域
$TTL 600
@ IN SOA dns.playground.com. dnsadmin.playground.com.(
20150305
1H
5M
3D
12H )
@ IN NS dns.playground.com.
40 IN PTR dns.playground.com.
12 IN PTR mail.playground.com.
13 IN PTR www.playground.com.
全部设置完成后,修改权限重启服务,然后开始测试
## 测试192.168.233.128
dig www.playground.com @192.168.233.128
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.30.rc1.el6_6.1 <<>> www.playground.com @192.168.233.128
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 38934
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 1
;; QUESTION SECTION:
;www.playground.com. IN A
;; ANSWER SECTION:
www.playground.com. 600 IN A 192.168.98.13
;; AUTHORITY SECTION:
playground.com. 600 IN NS dns.playground.com.
;; ADDITIONAL SECTION:
dns.playground.com. 600 IN A 192.168.233.128
;; Query time: 1 msec
;; SERVER: 192.168.233.128#53(192.168.233.128)
;; WHEN: Sat Mar 14 14:34:47 2015
;; MSG SIZE rcvd: 86
## 测试172.25.137.40
dig www.playground.com @172.25.137.40
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.30.rc1.el6_6.1 <<>> www.playground.com @172.25.137.40
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 12736
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 1
;; QUESTION SECTION:
;www.playground.com. IN A
;; ANSWER SECTION:
www.playground.com. 600 IN A 172.25.137.13
;; AUTHORITY SECTION:
playground.com. 600 IN NS dns.playground.com.
;; ADDITIONAL SECTION:
dns.playground.com. 600 IN A 172.25.137.40
;; Query time: 0 msec
;; SERVER: 172.25.137.40#53(172.25.137.40)
;; WHEN: Sat Mar 14 14:35:39 2015
;; MSG SIZE rcvd: 86
测试成功,我们可以看到,相同域名解析不同的IP
 运维那些事
运维那些事